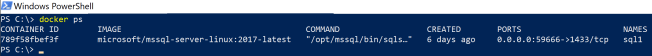
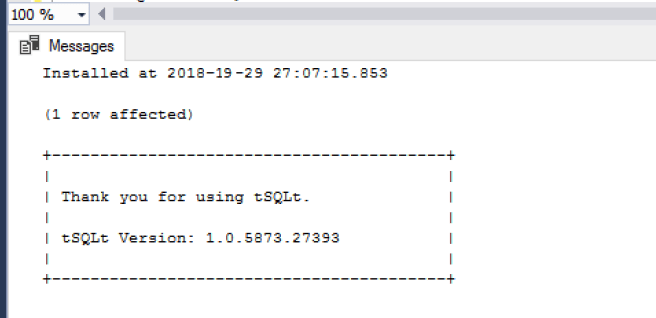
in my previous post I wrote about how easy it is to add the tSQLt unit test framework to your database if it is running in a docker container.
How to use tSQLt unit test framework with a SQL Server database in a docker container
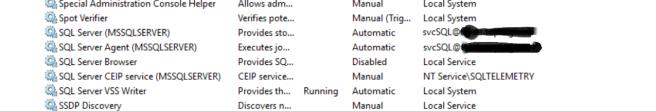
But let’s say you have the SQLTest utility from Redgate (hopefully you’ve bought the SQL Toolbelt as it really does make your life way simpler and more productive)
https://www.red-gate.com/products/sql-development/sql-toolbelt/index
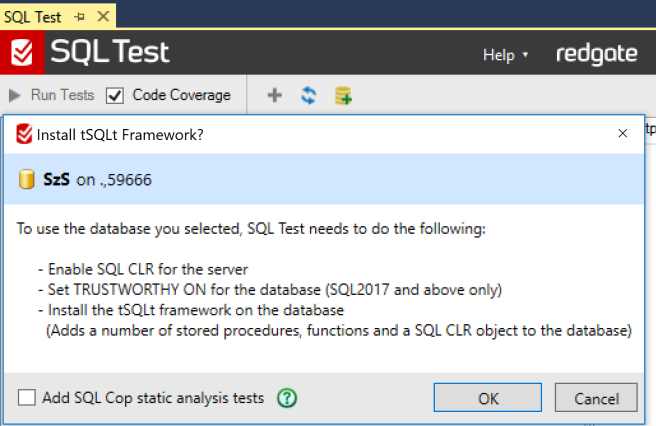
So as per usual – open up SQLTest and choose the database that you want to add the tSQLt framework (that is encapsulated in SQLTest) to;

You will be presented with this screen – I generally take off the tick for SQL Cop and add those tests later..
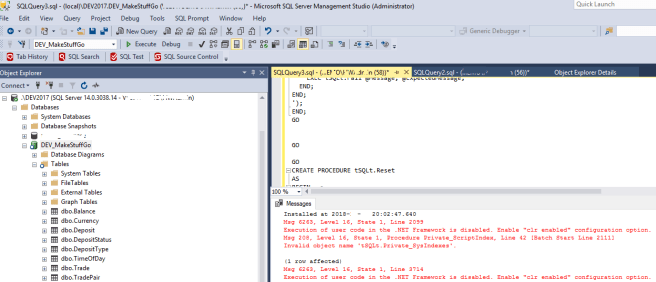
Error:
Unfortunately we get an error:

Resolution:
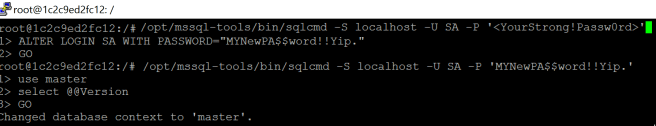
Basically we need to add tSQLt manually and edit some things to make it work with SQL Server running in a docker container:
1. First we need to ensure set both clr enabled and clr strict security to enabled:
EXEC sp_configure 'show advanced options', 1 RECONFIGURE GO EXEC sp_configure 'clr enabled', 1 EXEC sp_configure 'clr strict security', 0 RECONFIGURE GO
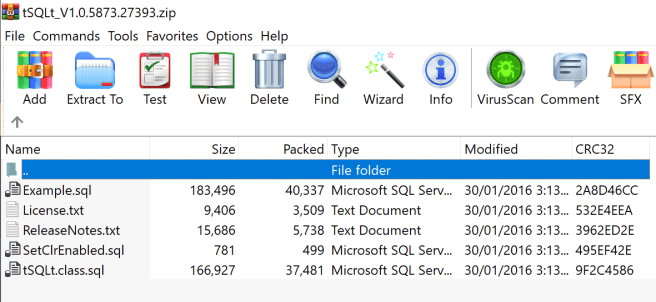
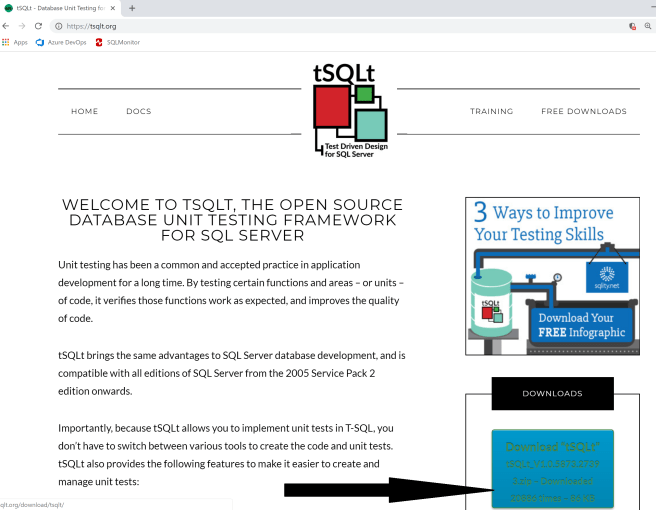
2. We can then either grab the script manually that SQLTest is using or manually download the tSQLt framework from http://tsqlt.org/download/tsqlt/
We will use the tSQLt.Class.sql script and basically search for:
PERMISSION_SET = EXTERNAL_ACCESS
and change it to
PERMISSION_SET = SAFE
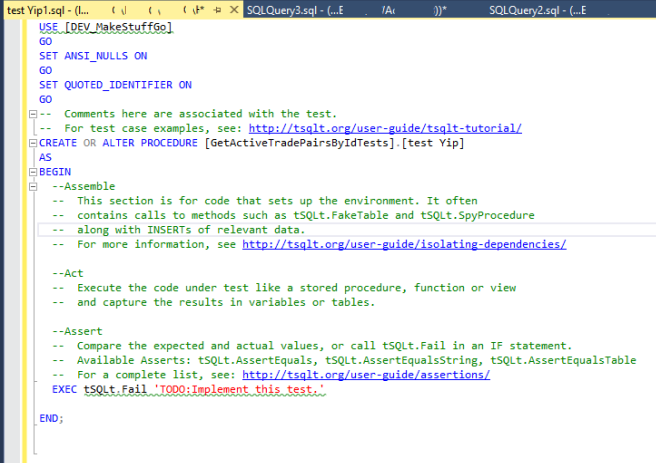
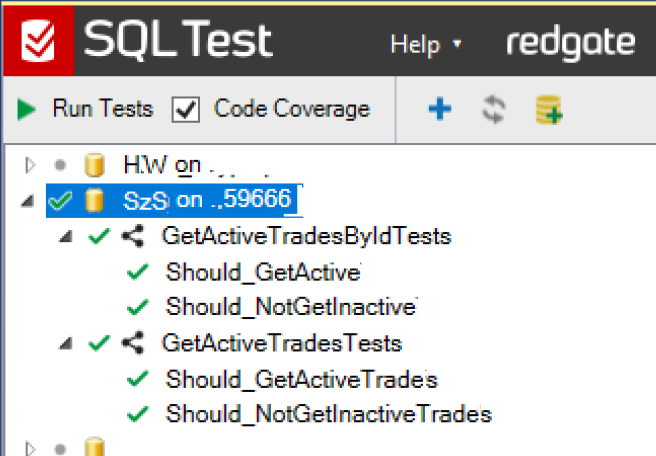
We can now either add our database to SQLTest as per normal (in fact if we’ve done everything correctly the it will just appear) so just try and hit refresh and your database should be there.
Now
There is now no reason at all that you should not be writing/running unit tests for your SQL code.
You can even do it against databases running in a docker container using SQLTest.
I always say unit tests are the thing that keep me employed – as all my buggy code (and there’s a lot) gets caught on my laptop (or container) and NOT in PROD or even UAT systems.
So go visit
https://tsqlt.org/user-guide/tsqlt-tutorial/
or these other great sites:
https://www.simple-talk.com/sql/t-sql-programming/getting-started-testing-databases-with-tsqlt
http://www.pluralsight.com/courses/unit-testing-t-sql-tsqlt
https://www.itprotoday.com/sql-server/getting-started-test-driven-design-sql-server
http://d-a-green.blogspot.co.uk/search/label/tSQLt
http://datacentricity.net/tag/tsqlt/
and in no time at all you will be writing your very own unit test.
Yip.